pyn3rd on Twitter: "#CVE-2022-41852 Apache Commons JXPath Remote Code Execution. We also can inject XPath expression with the JDBC attack gadgets which I have disclosed. https://t.co/VQcXyeieNW" / Twitter

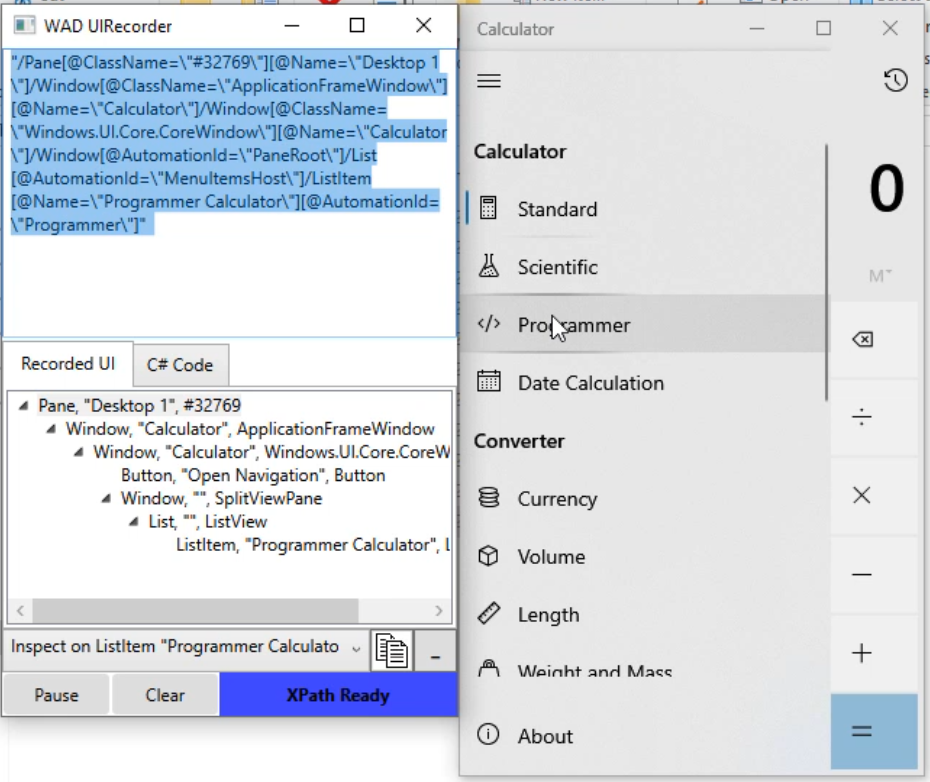
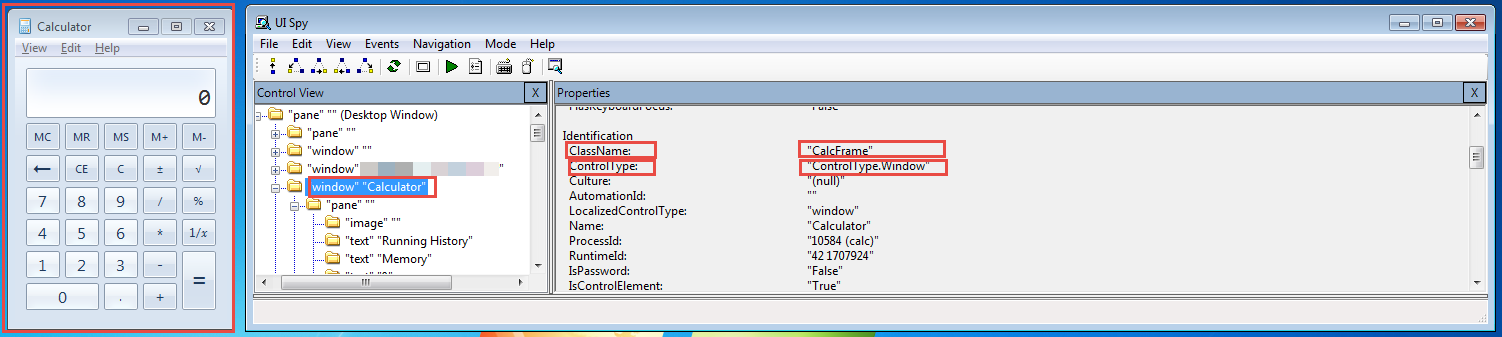
Software testing tutorials and automation: UI Automator Viewer : Get Android App Element's XPath, ID, Name And className